SeaGlass is a system designed by security researchers at the University of Washington to measure IMSI-catcher use across a city.
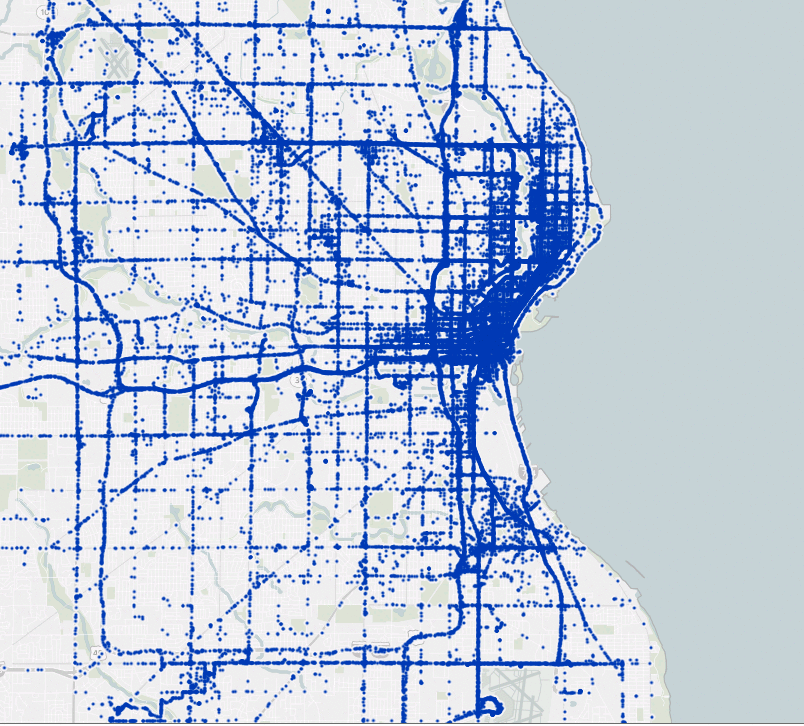
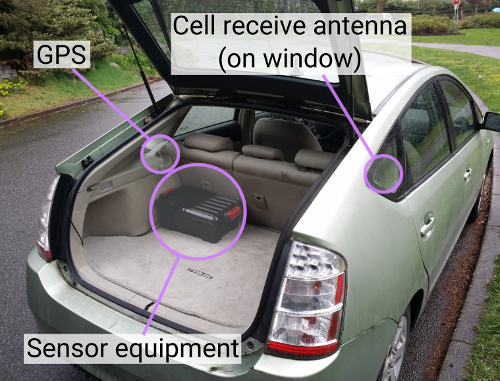
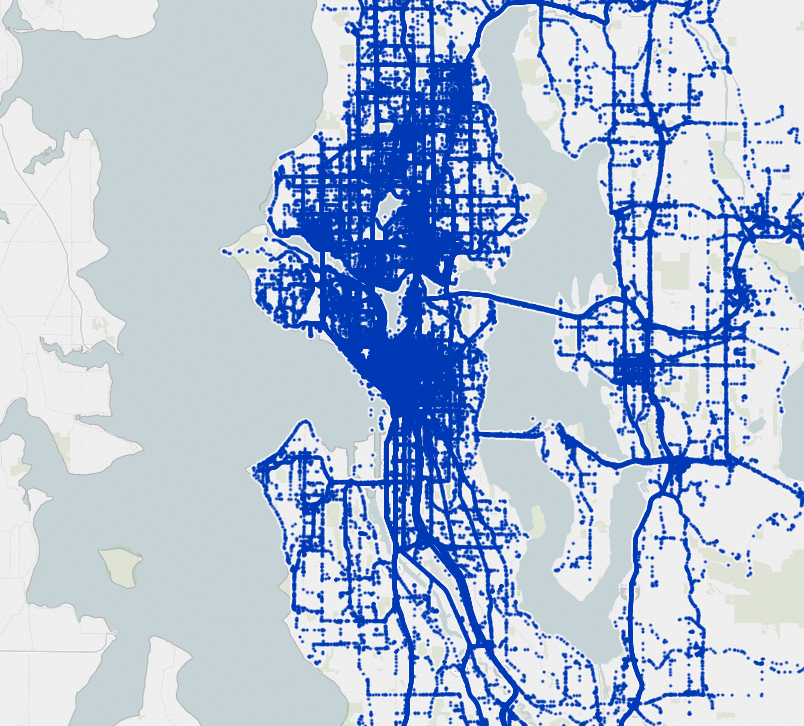
Cellular sensors are built from off-the-shelf parts and installed into volunteers’ vehicles

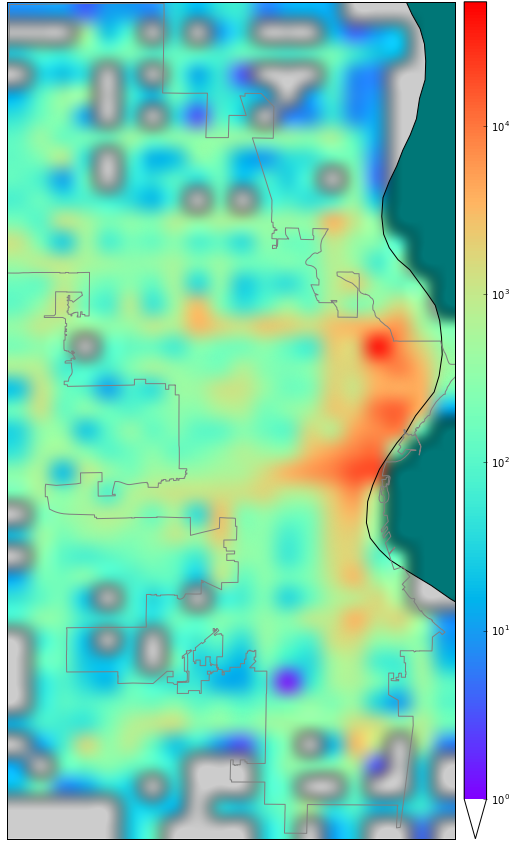
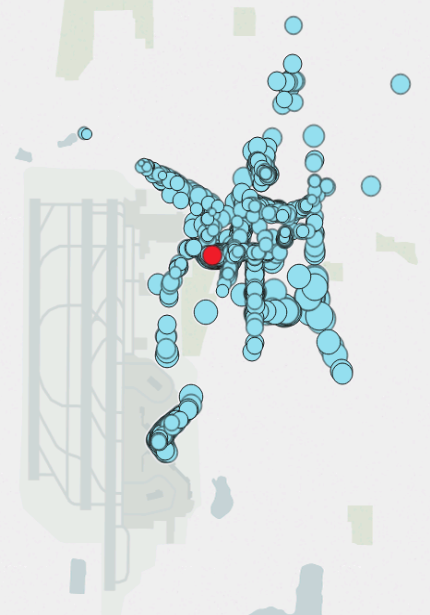
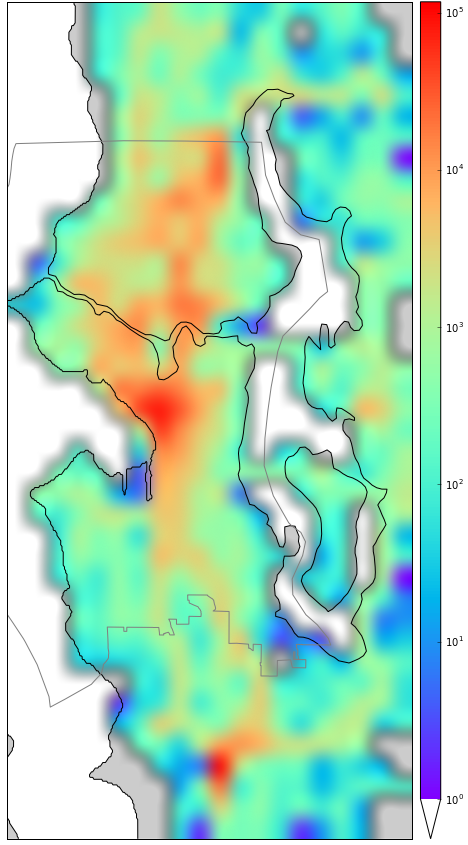
Sensor data is continuously uploaded from vehicles and aggregated into a city-wide view
Algorithms find anomalies in the cellular network that indicate IMSI-catchers

 Stingray II IMSI-catcher
Stingray II IMSI-catcher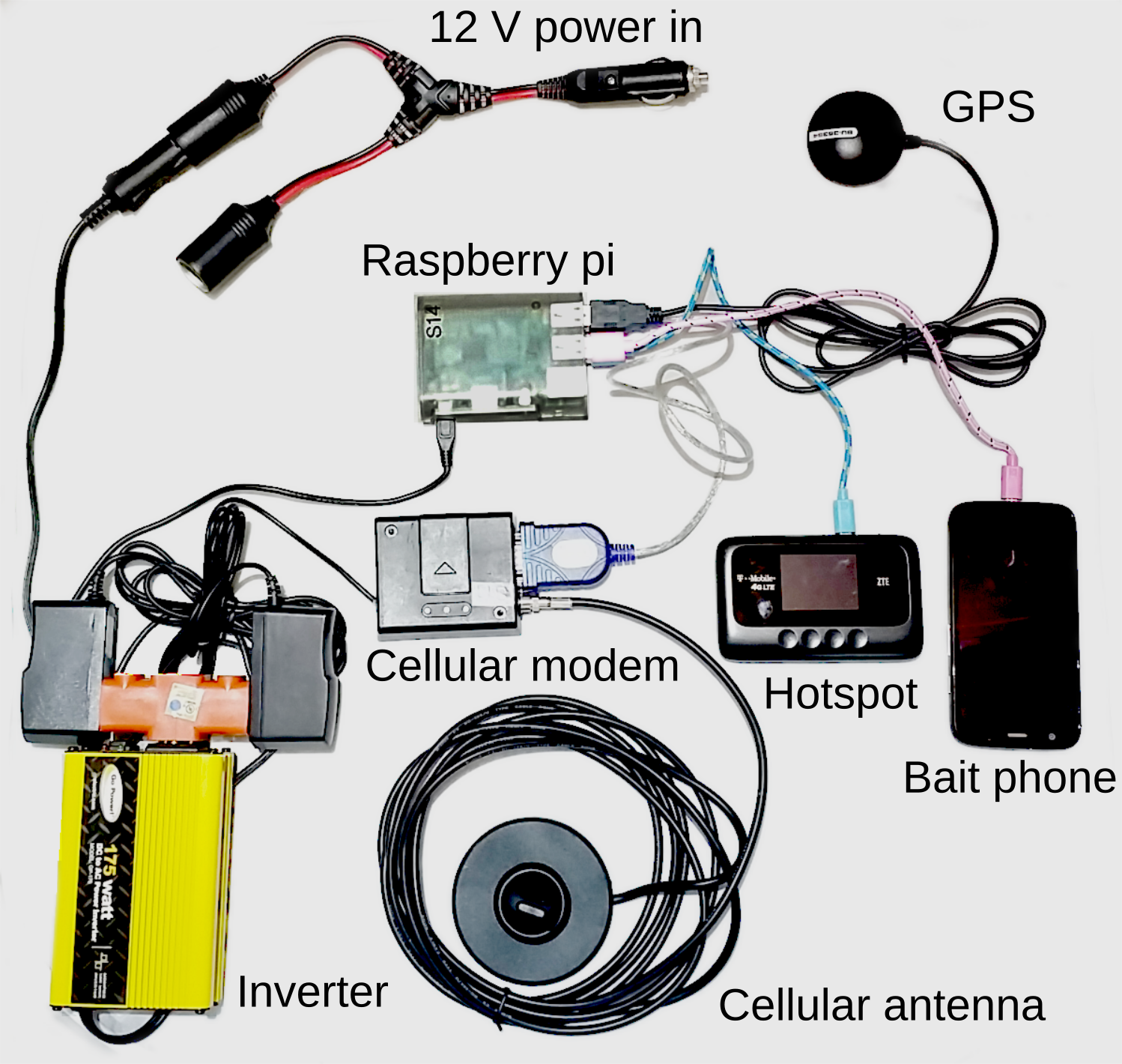
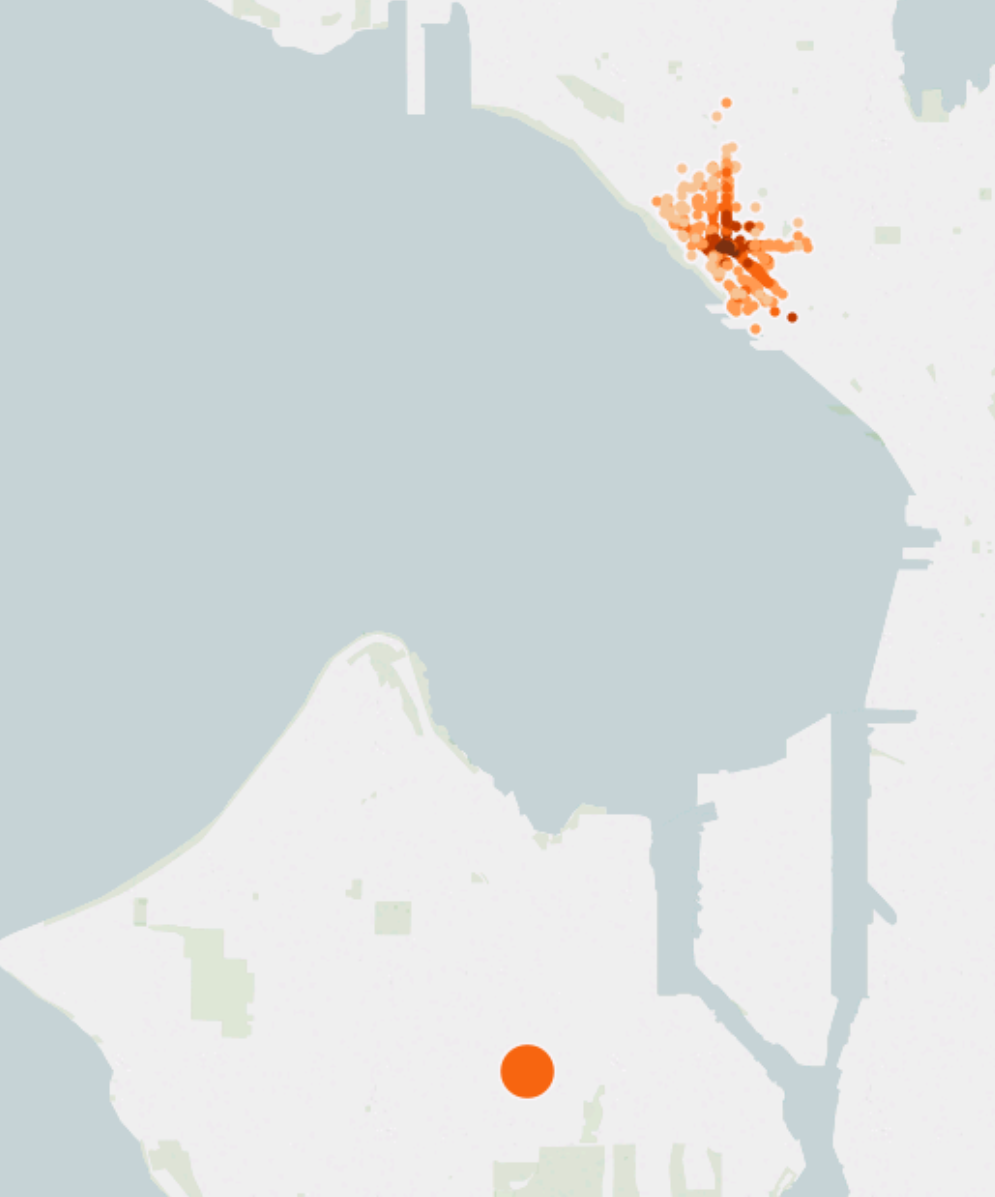
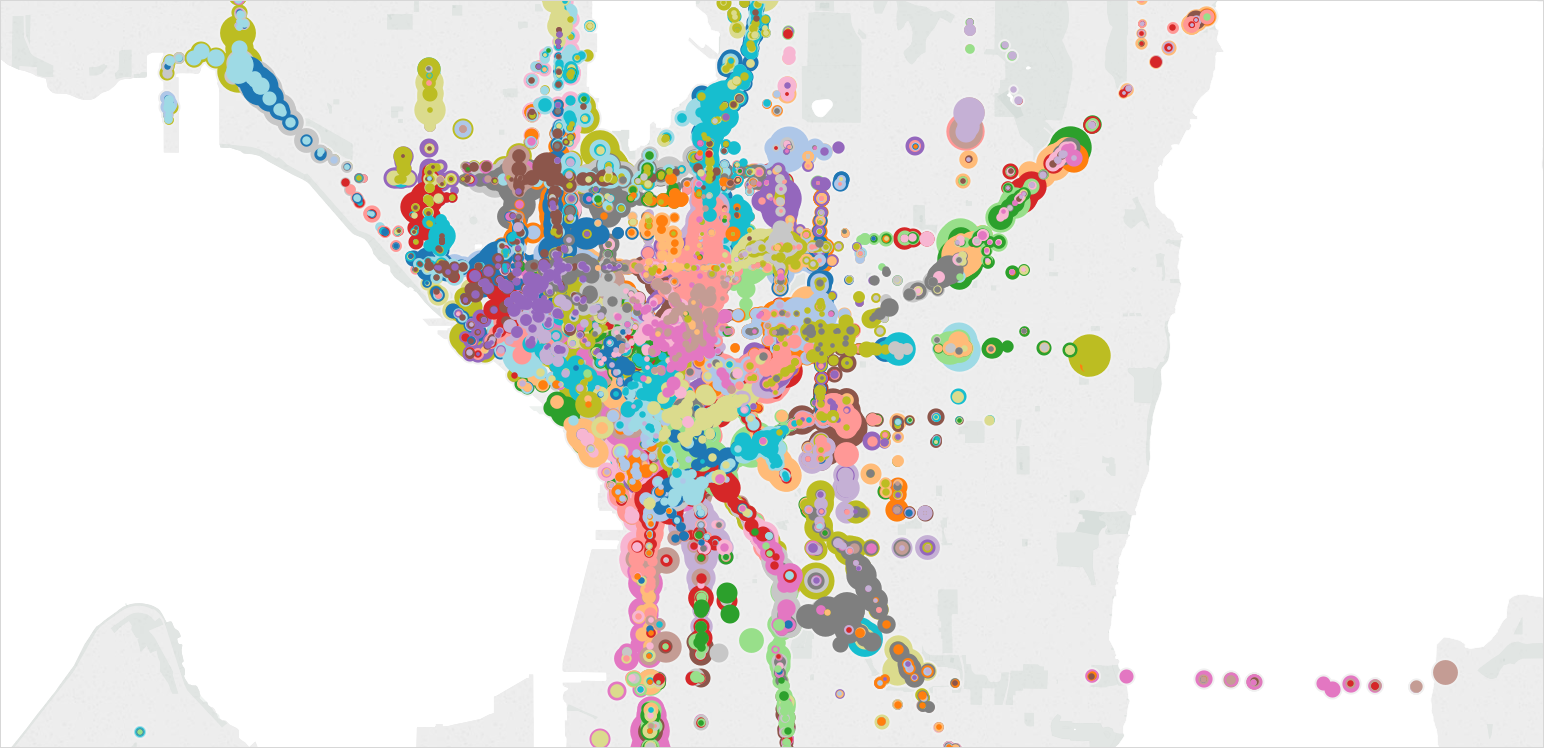
 Hover over image to zoom into downtown.
Hover over image to zoom into downtown.